Mobile Device Management Using Microsoft Intune
While our personal devices have certainly expanded our minds and talents, protecting sensitive data has become a real challenge for businesses.
Corporate Security vs Personal Life: the Ultimate Choice
In the last years, cyberthreats have grown a lot, making security a top priority for all companies.
Ask yourself a question: is there a room for coexistence, when we talk about corporate security and personal life? When employees work remotely or in a distributed environment, when personal devices with important corporate information may be lost, would you really want to let your employees use a personal laptop, tablet or smartphone as a working device?
At this point, it really comes down to a choice. You may trust your employees and do nothing about it. You may take a step further and introduce extreme measures, disallowing to use personal devices during working hours. Both approaches would be a sort of a double-edged sword.
Separating personal and corporate data, and protecting the latter – are the ultimate challenges if we want to keep things secure and employee-friendly. Microsoft Intune might be a perfect answer to these and other questions.
Guarding Corporate Secrets with Mobile Device Management
Bring Your Own Device (BYOD) is a relatively new corporate trend, alleviating security concerns and erasing borders between work and private life. Allowing personal devices for production needs is a perfect way to increase employees’ loyalty, which is important for any company.
While BYOD has many benefits, introducing BYOD poses security and manageability problems. There is always a chance that personal devices may be lost, stolen or infected with malware. That’s when Mobile Device Management comes to the rescue.
Nowadays, dozens of companies offer MDM services. Their solutions allow handling protection of the corporate information by configuring employees’ personal devices to comply with company’s policies. Instead of imposing extreme administrative measures, you raise your employees’ awareness about the corporate data security and let IT security specialists do the rest. Still, selecting a MDM and its proper setup is a rather challenging task.
In the following review, we’ll be setting up Mobile Device Management for SMBs with the help of Microsoft Intune.
What Is Microsoft Intune?
Microsoft Intune is a powerful cloud service for managing Windows, iOS, Android mobile devices and Windows-based workstations. It allows managing device settings, permissions and data encoding; restricting applications; remotely erasing device data in case it’s stolen; etc.
Some of Intune main advantages are:
- Ease of management – cloud service implies simplified deployment.
- Reliability – Intune receives constant updates and improvements from Microsoft.
- Scalability – the service is easily scalable.
While being rather flexible in terms of configuration, there are two primary setup versions:
- MS Intune Standalone version
- Hybrid model: Intune + SCCM 2012 OR Intune + SCCM 2012 + Azure
This time we’ll be focusing on the Standalone Version, which is more suitable for small-to-medium businesses.
Intune Service Sign Up
Intune service sign up procedure is simplified. With a monthly fee being $6.00 per user, Microsoft allows up to 15 devices per user and offers up to 20 GB of cloud space for applications.
To test the service, you can get up to 60 days of a trial period with the service limited to 100 concurrent users. After the initial 30 days of the trial period, you can extend it for another 30 days by providing the payment card details.
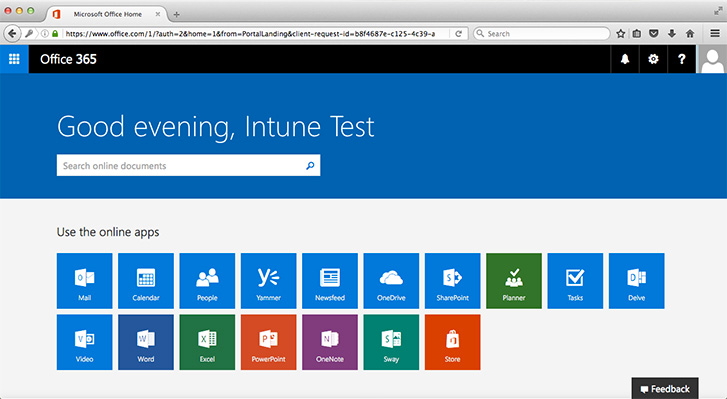
After the initial sign up, you get access to Intune Service Dashboard and Office 365 Portal.
The next step is to create a list of Intune app users. To create or import new users, administrators should use Office 365 Portal. The default login format for each user can be either UserName@CompanyName.onmicrosoft.com or can be based on a company domain name.
MDM Process
The Mobile Device Management process can be divided into 5 main stages:
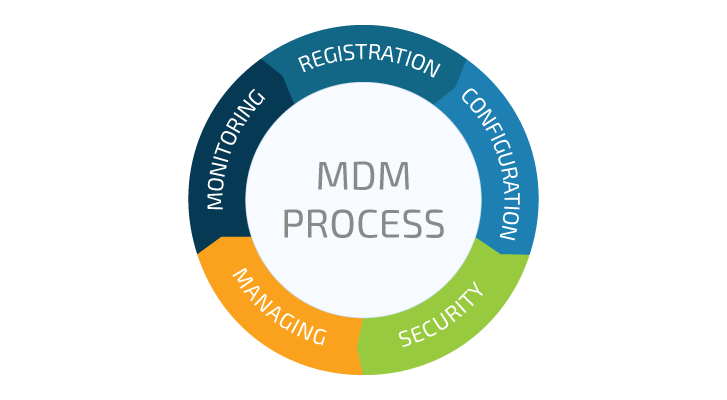
Let’s review each of them one by one.
User Registration
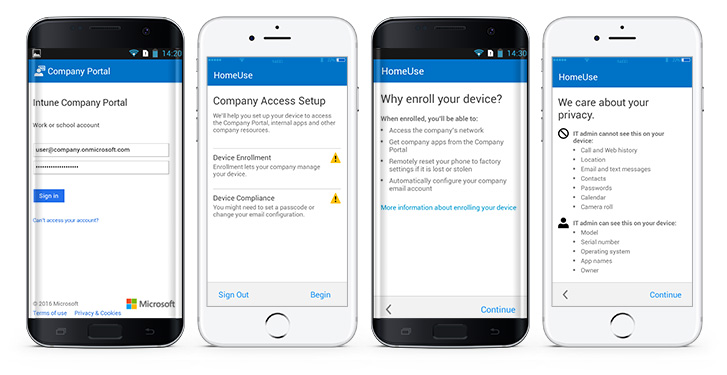
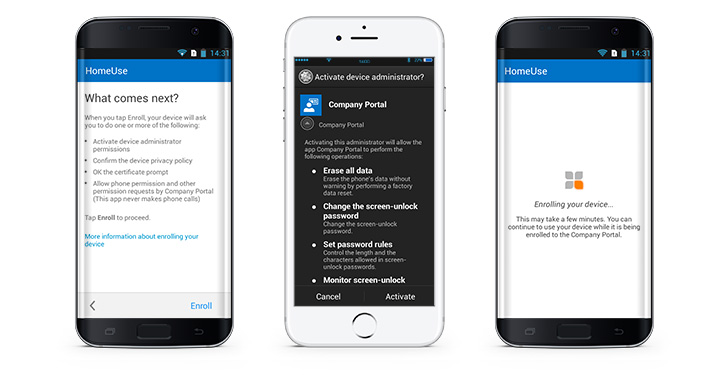
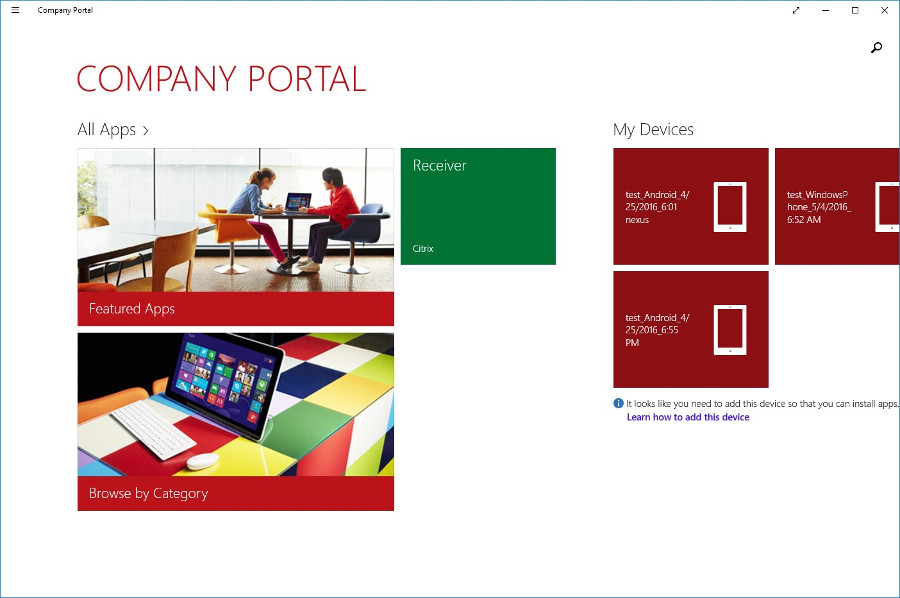
Registration requires installing Company Portal application on a user’s device:
To facilitate communication with users, Microsoft offers some basic guides for administrators that may come in handy while registering devices in Intune and solving various tasks after the registration.
After the initial app installation and logon, a device is enrolled for management with Intune.
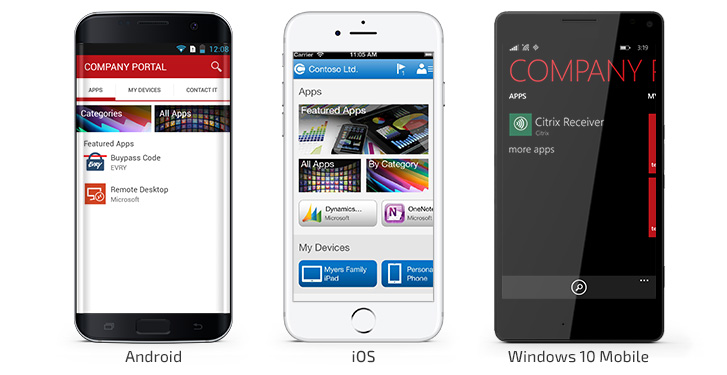
Supported Platforms and Intune App Overview
As of now, Intune supports iOS, Android, Windows 8.1 and 10, and Mac OS X devices.
The Company Portal application contains three main sections:
- Applications – the list of applications available to a user
- My Devices – the list of user’s devices (15 max.)
- Contact IT service – contact information to get in touch with the IT service
A device can be managed immediately after the initial registration. All registered devices and users are added to the corresponding branches in the “Groups” page found on Dashboard. Administrator can group devices and users by various criteria or directly assign group membership for further sharing group management (similar to collections in SCCM 2012).
Windows 10:
Mac OS X:
Application Deployment
Intune supports installation of applications from app stores, web applications, and in-house apps.
Currently, it’s possible to install apps in two ways:
- Via an Installer – you’ll need an installation file for an application, e.g. APK for Android.
- Via an External link – you’ll need to provide a link to an application in the app store.
Let’s review both ways in the guides below.
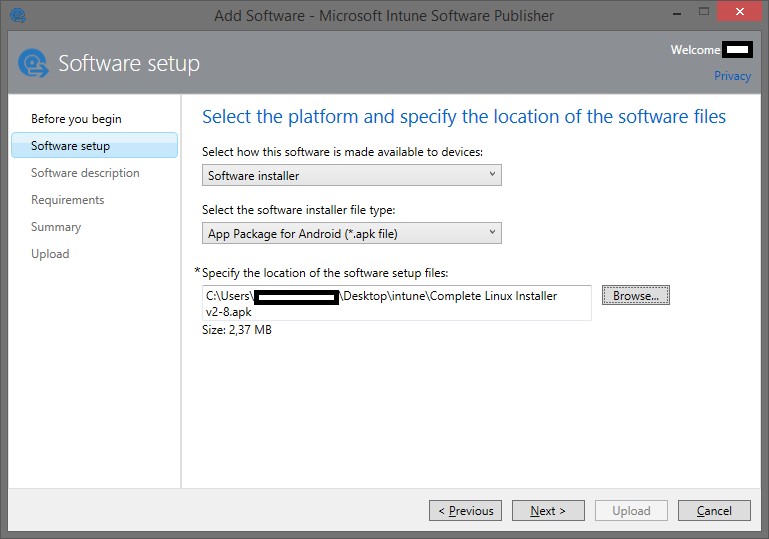
A guide on adding an application to MS Intune via installer:
1) Choose an installation file:
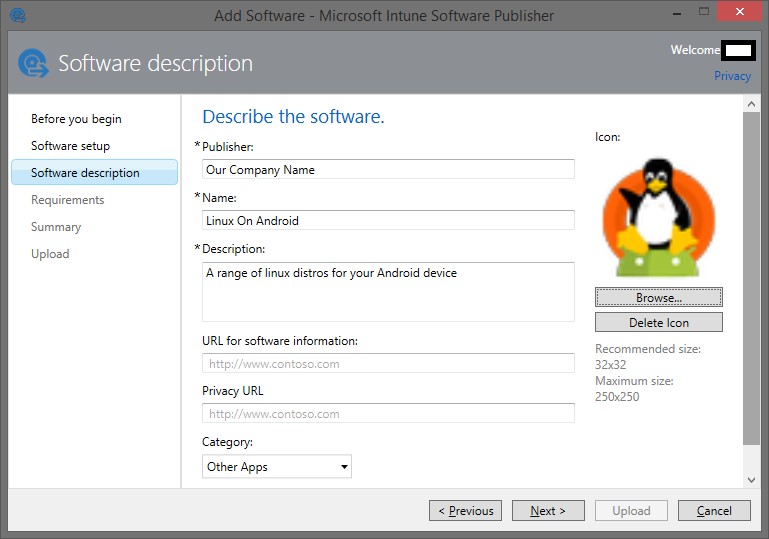
2) Fill in the software description:
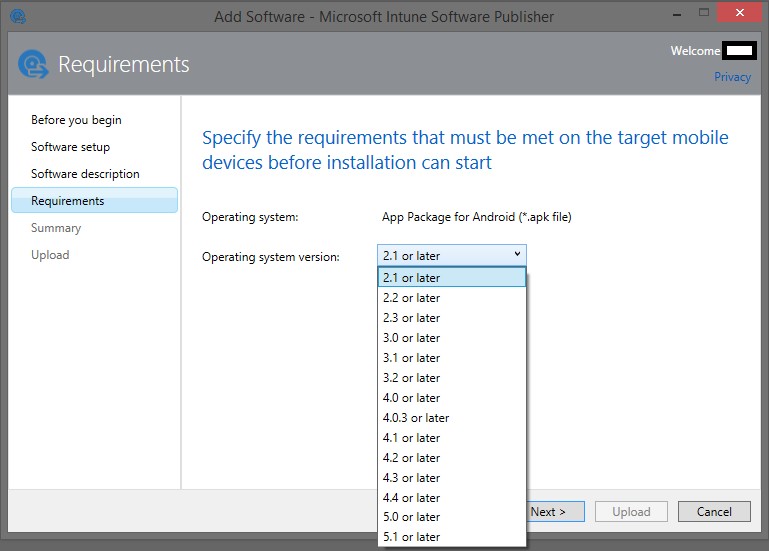
3) Specify user device OS requirements:
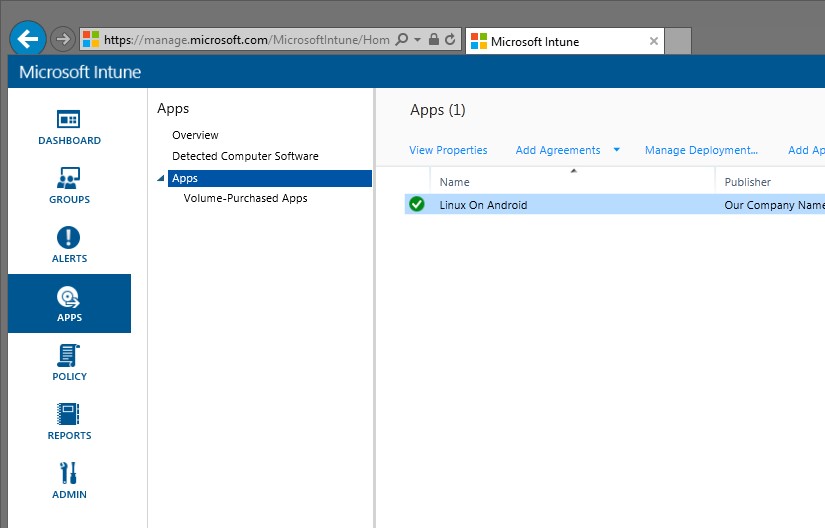
4) Application is added to the application list on Dashboard:
A guide on adding an application to MS Intune via external link:
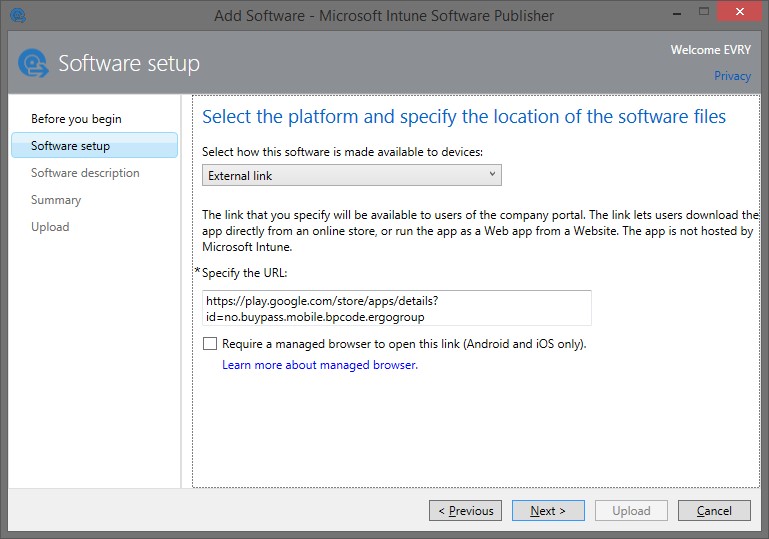
1) Specify the link to an application in app store:
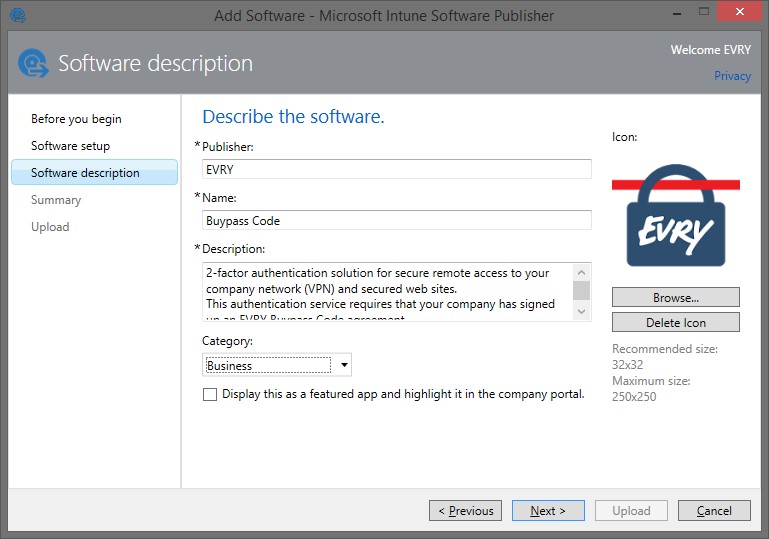
2) Fill in the software description:
3) After adding an application to the application list, you’ll need to deploy it to user devices.
Select “Manage Deployment…” from the context menu and assign application to a group of users or a group of devices.
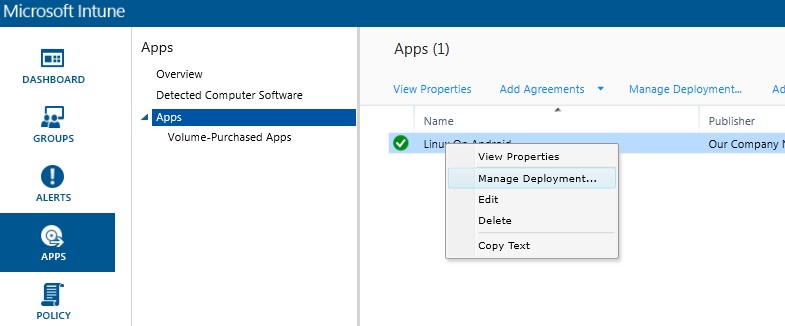
4) The following options are available for applications deployment:
- Required Install
- Available Install
- Uninstall
5) The application assigned to a certain group will appear on users’ devices.
Configuration
Intune security options allow creating flexible configurations, policies and operation modes on users’ devices:
- Device settings, such as permission to use Bluetooth, Camera, NFC, etc.
- Password settings, including password length and its strength
- Encoding settings
- Browser settings, such as restriction on saving cookie, blocking jscripts, etc.
- Allowed and restricted applications.
Naturally, the list of available settings is different for each major platform and may be different for each version of the platform. Thus, an administrator may have hard time to setup all devices of company employees, if they all use different platforms. A list of prompts with minimal platform requirements may be of help in this case.
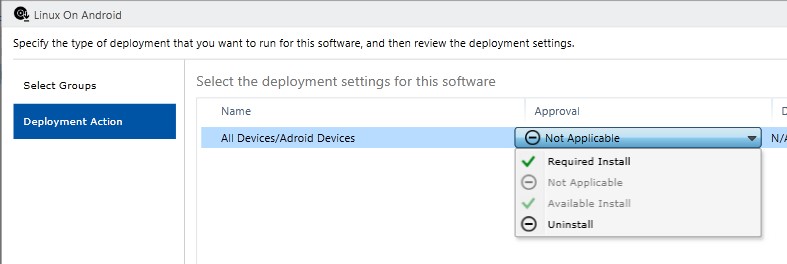
Next, let’s review a user policy tweak on example of Device Camera Restriction:
When the camera is launched, a user will receive the following security notification:

Please note again, that although Intune offers a wide range of device configuration parameters, availability of some options varies with device. In most cases, this can be resolved by tweaking OMA-URI parameters – a common standard for configuring mobile devices to set necessary values.
Monitoring
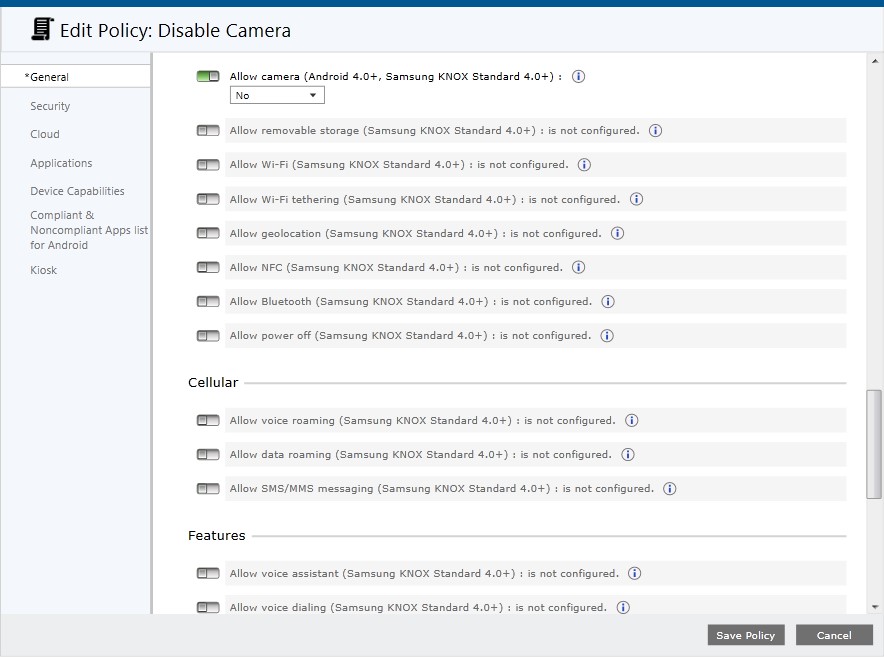
After deploying applications and policies, administrator can monitor device status.
The “Dashboard” page shows a general status of all components
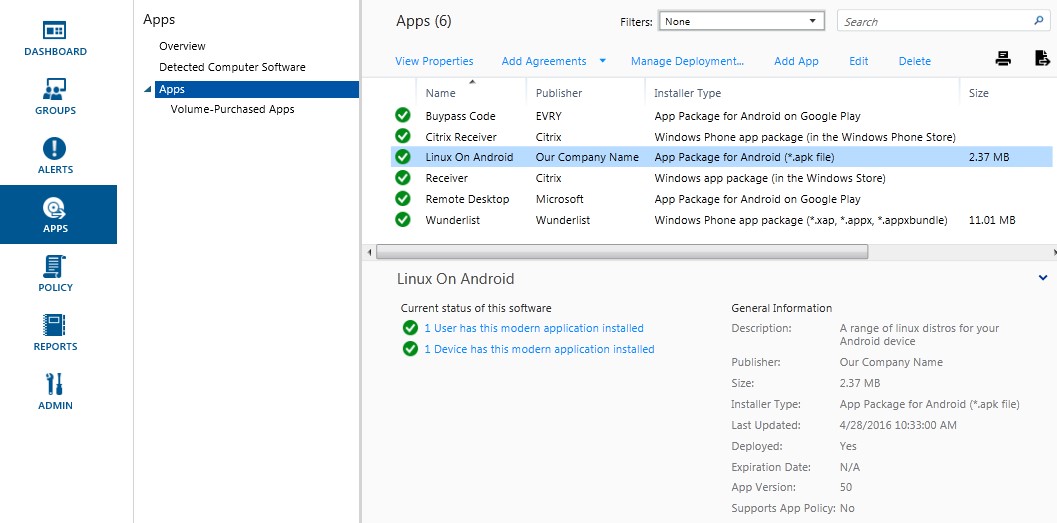
Detailed information on application statuses is available on “APPS” page
Clicking on an application will show some general information about it:
Administrator will immediately receive a notification in case of malicious activities and incidents, such as conflicts between Intune policies or alarms about malware on a PC.
A quick filters list can help you locate certain devices based on their statuses:

Security
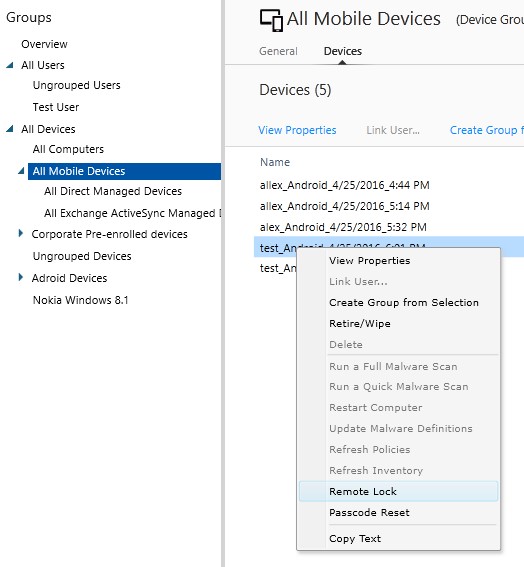
In case a device is lost or stolen, it is possible to wipe all corporate data or even all information from the device.
You can also reset the passcode or lock the device remotely.
To do this, select a user, pick one of the devices and select an action from the context menu:
Conclusion
This short guide covers the basics of Mobile Device Management with Microsoft Intune. It is worth mentioning that over the last years Microsoft Intune has matured enough to be used for enterprise needs. It is one of a few stable solutions currently available with full-scale support and updates. Moreover, it can be integrated with SCCM, making it the best option for large corporations.
N.B.: catching up with technological advances is never easy. This year has seen the dawn of the mixed-reality devices such as Magic Leap and Microsoft HoloLens, allegedly coming to the mass market next year and possibly changing our perception of personal computing. A sound idea would be to have a certain tactic from the very beginning and follow it, before the storm hits with full force. While new technologies are yet to arrive, companies still have some room to design appropriate device management strategies.
Useful resources
Do you use Intune for corporate purposes? Please share your thoughts in the comments.

![Cloud-Native Maturity Model Assessment [thumbnail]](/uploads/media/thumbnail-280x222-what-Is-the-cloud-native-maturity-model-definition-and-assessment-criteria.webp)
![AI in Telecom [Thumbnail]](/uploads/media/thumbnail-280x222-ai-in-telecom-network-optimization.webp)
![Containers vs VMs for Microservices [thumbnail]](/uploads/media/thumbnail-280x222-containers-vs-vms-what’s-better-for-microservices.webp)
![Accelerated Development with Azure DevOps Toolset [thumbnail]](/uploads/media/thumbnail-280x222-how-to-improve-developer-velocity-with-azure-devops.webp)
![10 Lessons Learned: AWS Migration [Thumbnail]](/uploads/media/thumbnail-280x222-10-lessons-learned-on-aws-migration.webp)

![Azure Backup for SAP HANA databases [Thumbnail]](/uploads/media/thumbnail-280x222-azure-backup-the-most-suitable-solution-for-sap-hana-databases.webp)
![Multi-Cloud Governance: Policies [thumbnail]](/uploads/media/thumbnail-280x222-multi-cloud- governance-policies-and-procedures.webp)
![Security Operations vs Security Development [thumbnail]](/uploads/media/thumbnail-280x222-how-to-strike-a-balance-between-security-operations.webp)
![Cloud-Native Development Challenges [thumbnail]](/uploads/media/thumbnail-280x222-challenges-of-cloud-native-application.webp)