Manufacturer of electric cars
Location:
Germany
Industry:
Automotive
About the Customer:
Development of a concept of over-the-air (OTA) solution, which allows distributing software updates over a wireless network without the need of a physical access to a vehicle. A manufacturer can remotely deliver firmware updates, patches, software and data updates to a vehicle removing the need for a driver to contact a dealer or a repair shop.
Business Challenge
- Software Update delivery guarantee. Even when Wi-Fi is not available, critical updates still must be delivered via LTE or 3G network as soon as possible. Solution must enable updates staggering to avoid cellular networks overload, especially when vehicles are often clustered in urban centers.
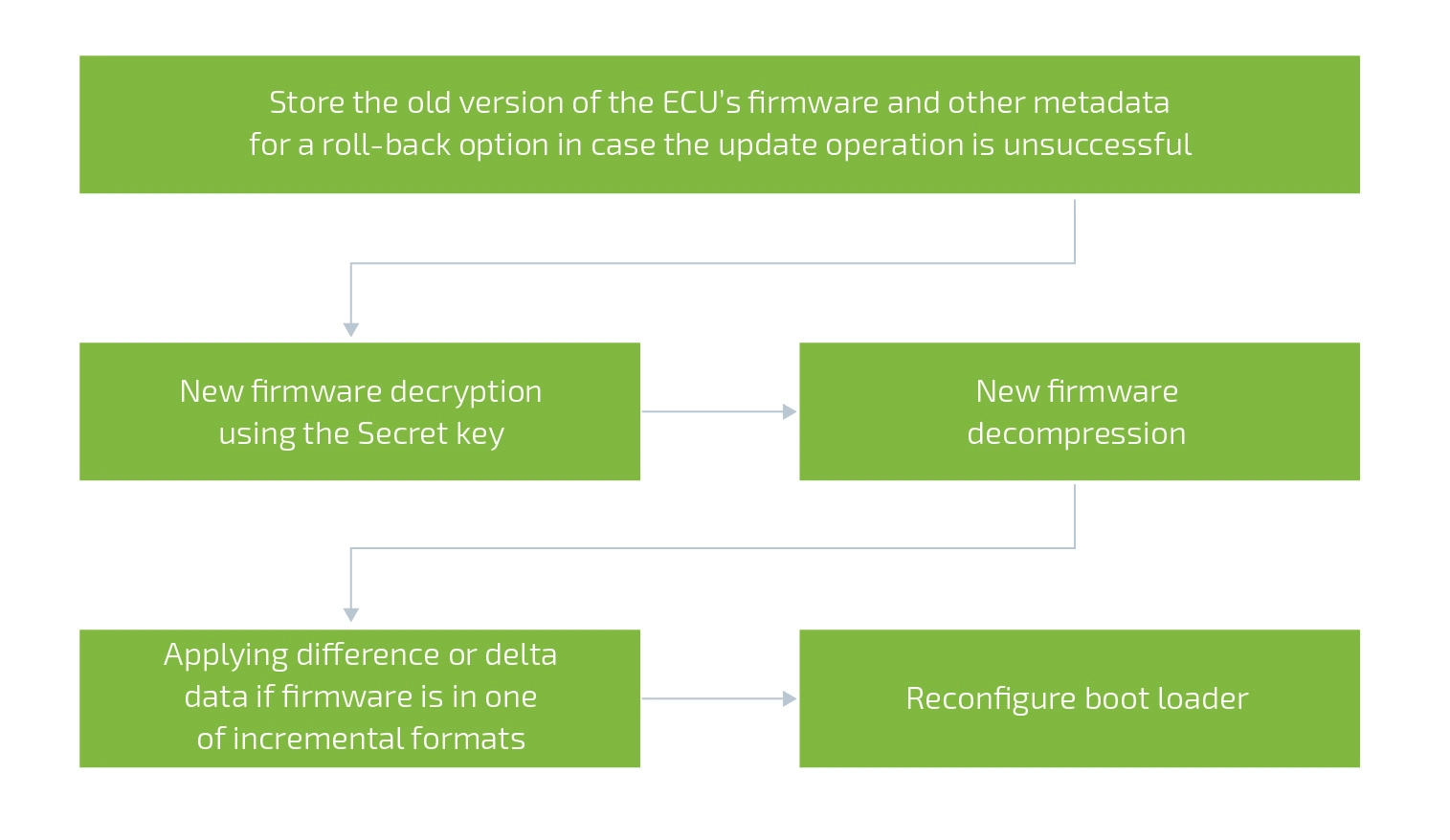
- Software Update installation reliability and rollback. Installation must not fail under any conditions, as there is no personnel to fix it. Thus, engineers of OTA Update follow the highest standard of update reliability by verifying sustainability on every step. If software update is interrupted due to any external factors, a system is designed to roll back to the previous state from the backup.
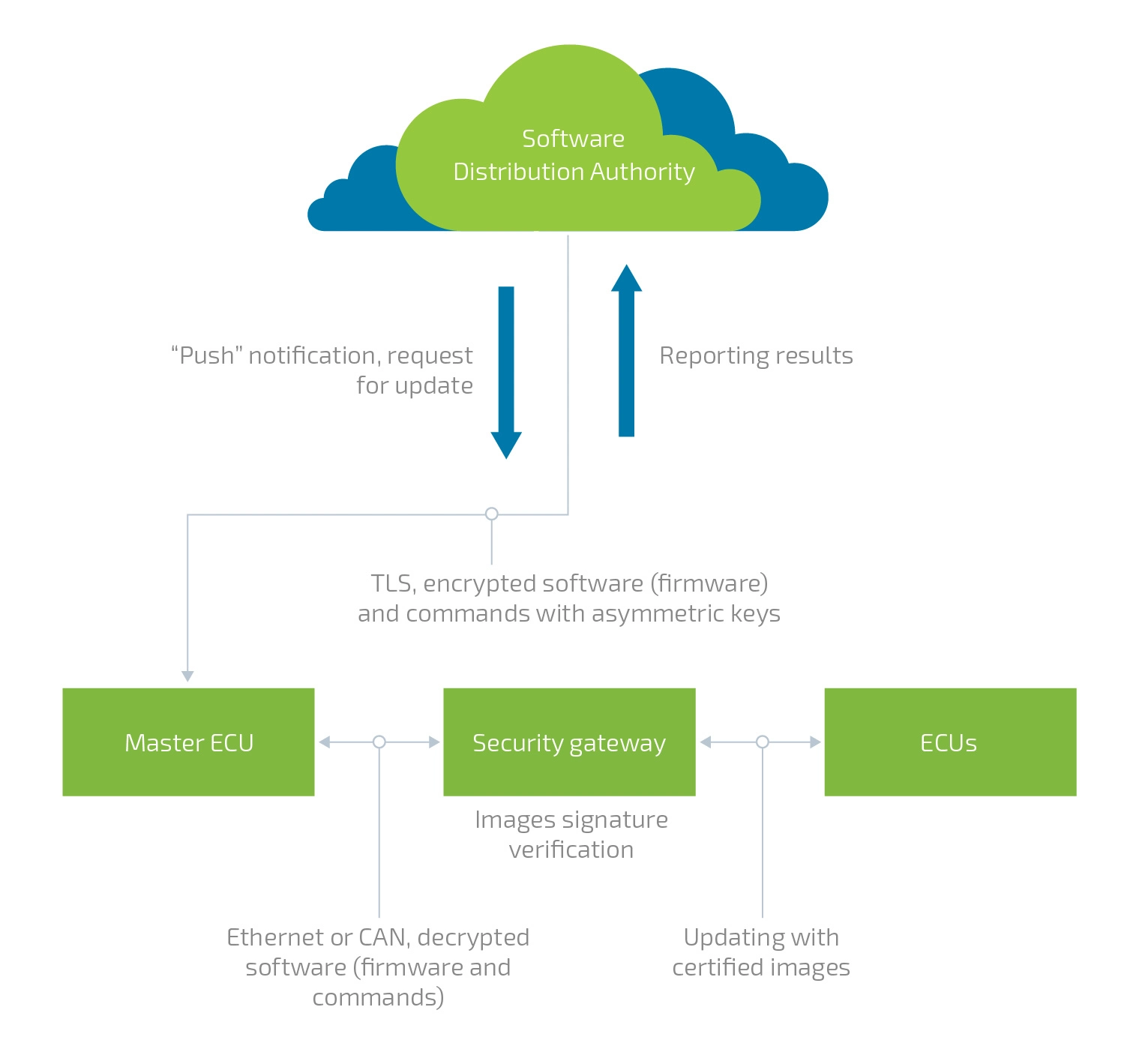
- Over-the-air update must be secure. The goal is to eliminate any issues related to ensuring safe vehicle-to-cloud communications. The team had to figure out how to enable an intact exchange of firmware, software and their meta data between OEM, Tier 1 and the Security Gateway ECU. Moreover, there were also other concerns regarding update package authenticity and integrity (data modification or data forging), authentication, and confidentiality.
- Fleet management. Also, the updates must be applied timely to large fleet of vehicles. Special campaigns were designed in order to monitor and control the status of software update distribution among vehicles in respect to model, market and other criteria.

Solution
Development of a concept of over-the-air (OTA) solution, which allows distributing software updates over a wireless network without the need of a physical access to a vehicle. A manufacturer can remotely deliver firmware updates, patches, software and data updates to a vehicle removing the need for a driver to contact a dealer or a repair shop.
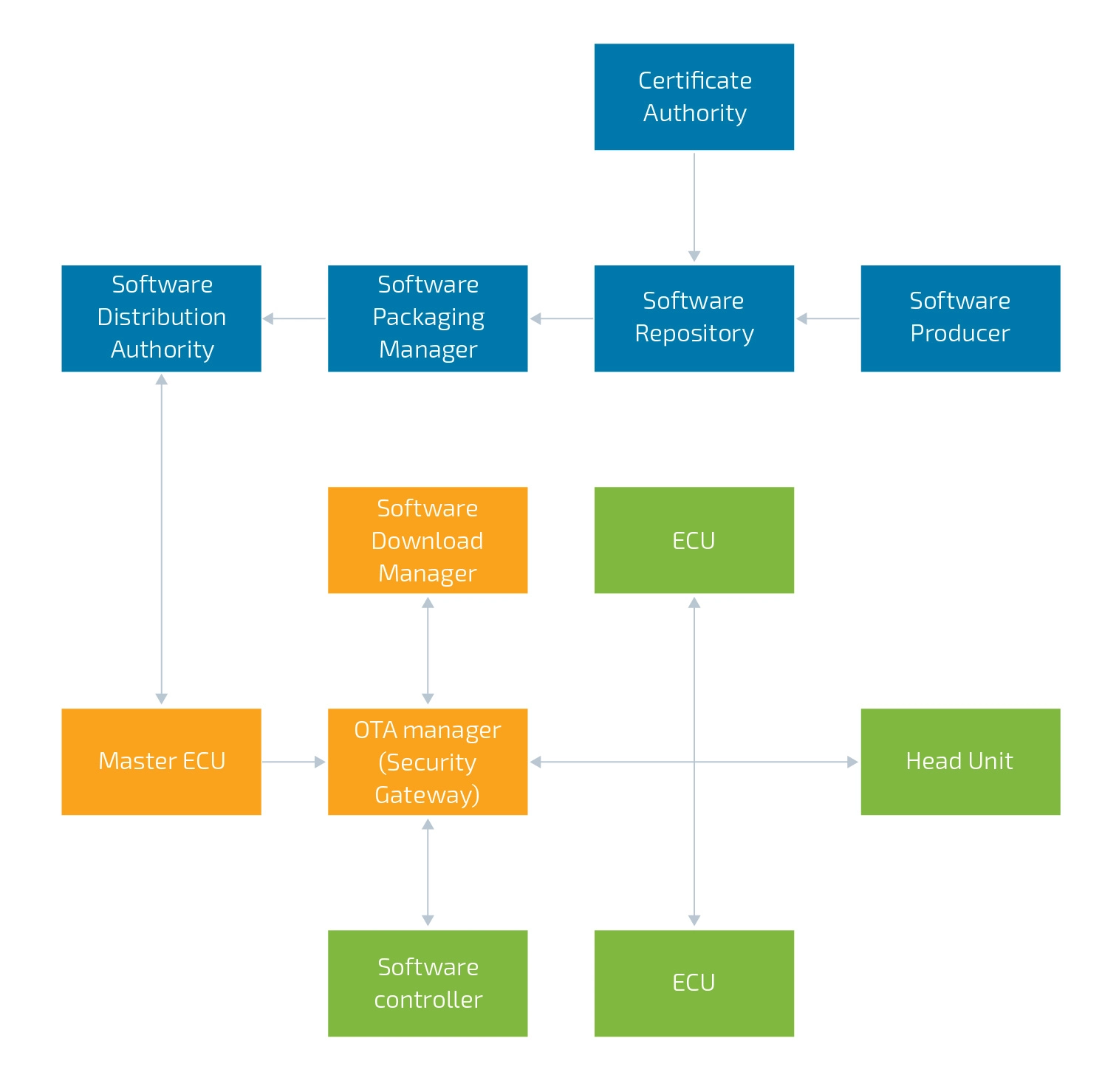
Our team has selected the following OTA update flow based on its three key points:
- Generating and storing software versions in the cloud-based Software Repository.
- Uploading OTA required software into the local vehicle storage.
- Installing new software and/or updating ECUs.
OTA Update Flow
OTA Security Approach
Generic Firmware Installation Process
Business Value
- Automating software-based recalls to resolve software defects
- Upselling new or existing features to increase subscription revenue
- Cost-effective updates of vehicle software and firmware
- Managing much shorter lifecycle of software and firmware
- Tracking ECU software down to the VIN, including software dependencies
- Reducing warranty costs for OEMs
- In-time updates stand for greater flexibility in the supply chain
- Improved vehicle security due to timely keys updating, security libraries updating, zero-day vulnerabilities patching
- Enhancing a driver’s satisfaction and brand loyalty
Technologies






Related Services
We have a solution to your needs. Just send us a message, and our experts will follow up with you asap.
Thank you!
We have received your request and will contact you back soon.