Hooking is Simple (Part 2)
Earlier I wrote an introductory article about hooks (their essence, functioning, Hello world). The article was supposed to be simple and minimalistic and it, basically, is. The only negative comment I received was: “Why use Microsoft Detours library? Its commercial version costs 10,000$!” That is quite a reasonable comment. This article will illustrate the procedure described in the previous article but using the madCodeHook library, which is about 20 times cheaper.
I recommend reading the introductory article first for better understanding of this one.
madCodeHook
This library has been around for a while. Its first version was released in 2000 and was meant for Delphi. It was not very functional at first, but since then it has been developed quite well: the authors have created SDK for C++, introduced support for 64-bit systems, all versions of Windows (Windows 9x — Win 8.1), came up with the driver to place hooks in all new processes and have regularly updated the library. The free version of the library was terminated as the authors did not want it to be a tool for hackers. But with the price starting with 349 EUR, this library is a perfect alternative to an extremely expensive Microsoft Detours, as well as to not user-friendly mhook and to unstable (in my experience) EasyHook.
Limitations of the evaluation version:
- no source codes
- no static linking
- you have to manually launch exe, which comes with the library
- you have to copy the madCHook.dll library to System32 beforehand
All in all, the limitations of the evaluation version are not critical if you want to see what it is all about. If you want to use it for commercial purposes, you’d better buy the licensed version.
Our objective
Our first article demonstrated how to use hooks to make Mozilla browser write “Привет, Хабр!” (Hello, Habr!) in its title when you log onto habrahabr.ru. So I will keep this objective for 2 reasons: firstly, I don’t feel like making up a new objective and, secondly, it will be useful to achieve the same objective using a different library. In such a way we can compare the processing speed, code size and complexity. The first article showed what hooks to place and where, so we’ll not discuss that here.
Procedure
- Download the latest version of madCodeHook and install it.
- Create a two-project solution in Video Studio (I am using VS 2010 but any other version is fine). The first project is the library with the hook code, which we will inject into browser’s process. The second project is the injector application, which will place the library into the browser’s address space.
- To create the first project, follow: File -> New -> Project. Type: Visual C++ -> Win32 -> Win32 Project. Choose “Dll” in the dialogue box.
- To create the second project, follow: File -> Add -> New Project. Type: Visual C++ -> Win32 -> Win32 Console Application.
- Find the header file and the lib-file in madCodeHook SKD and place them into the projects. After installing the library these files are found by default at C:\Program Files (x86)\madCollection\madCodeHook\Dll. The evaluation version of the library permits only dynamic linking, so take the following files: madCHook — dynamic.h and madCHook — dynamic — microsoft.lib. It’s possible to rename the files for convenience into madCHook.h and madCHook.lib.
- Write the code. The key moments are the following:
- Injector code:
#include “stdafx.h”
#include
#include “windows.h”
#include “madCHook.h”
#include
HANDLE GetProcessByName(PCWSTR name)
{
DWORD pid = 0;
HANDLE snapshot = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);
PROCESSENTRY32 process;
ZeroMemory(&process, sizeof(process));
process.dwSize = sizeof(process);
if (Process32First(snapshot, &process))
{
do
{
if (_wcsicmp(process.szExeFile, name) == 0)
{
pid = process.th32ProcessID;
break;
}
} while(Process32Next(snapshot, &process));
}
CloseHandle(snapshot);
if (pid != 0)
return OpenProcess(PROCESS_ALL_ACCESS, FALSE, pid);
return NULL;
}
int _tmain(int argc, _TCHAR* argv[])
{
InjectLibraryW((DWORD)GetProcessByName(L”firefox.exe”), L”HookLib.dll”);
_getch();
UninjectLibraryW((DWORD)GetProcessByName(L”firefox.exe”), L”HookLib.dll”);
} - Code of the library with the hook:
#include “stdafx.h”
#include “madCHook.h”
LRESULT (WINAPI * TrueSendMessageW)(HWND hWnd, UINT Msg, WPARAM wParam, LPARAM lParam) = SendMessageW;
__declspec(dllexport) LRESULT WINAPI MySendMessageW(HWND hWnd, UINT Msg, WPARAM wParam, LPARAM lParam)
{
if (Msg == WM_SETTEXT && wcsstr((LPCTSTR)lParam, L”Хабрахабр”NULL)
return TrueSendMessageW(hWnd, Msg, wParam, (LPARAM)L”Привет, Хабр!”);
return TrueSendMessageW(hWnd, Msg, wParam, lParam);
}
BOOL APIENTRY DllMain(HMODULE hModule, DWORD ul_reason_for_call, LPVOID lpReserved)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
HookAPI(“User32.dll”, “SendMessageW”, MySendMessageW, (PVOID*) &TrueSendMessageW);
}
return TRUE;
} - Find a ready-made project on Githab here.
- Injector code:
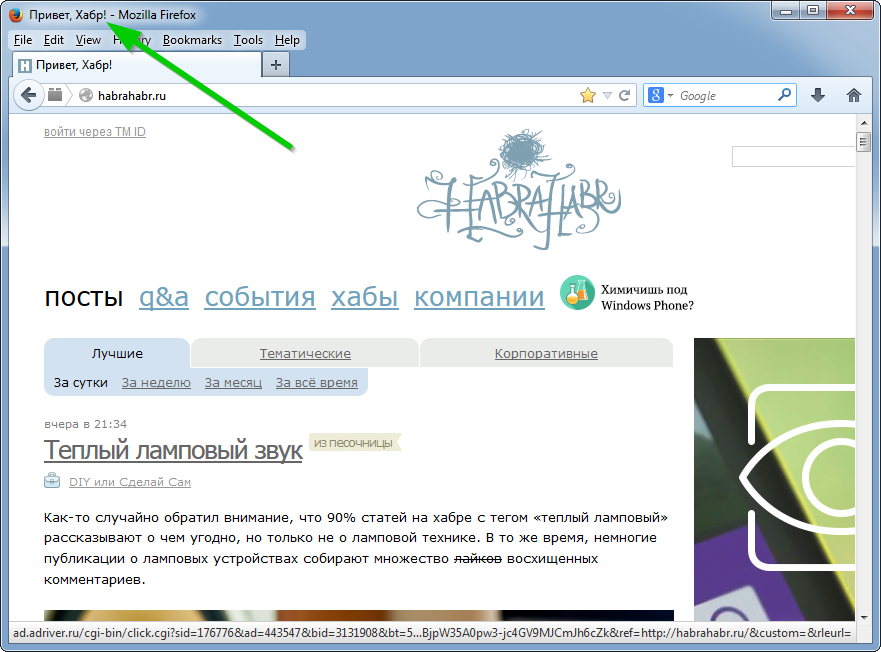
- Compile, launch Firefox, launch mchEvaluation.exe, launch the injector, log onto habrahabr.ru in the browser. The result is the following:
Conclusions
The madCodeHook evaluation version is not as user-friendly as that of Microsoft Detours, although full versions of these libraries are almost the same. In terms of writing a code, madCodeHook requires less of it, as it has a driver to introduce libraries into all running processes as well as into new ones, while Microsoft Detours needs a separate service or a driver to do it. In terms of processing speed and stability, both libraries seem similar. madCodeHook does not look as “enterprised” as Microsoft Detours, which is its advantage and disadvantage at the same time. On one hand, you can contact madCodeHook authors on their forum, which is good, but on the other – you find the I-can-leave-for-a-6-week-vacation-anytime-during-the-year note there, which is bad. The madCodeHook community can be reached at their forum, while the Microsoft Detours community is scattered among Stackoverflow, wasm.ru and MSDN forums, and seems to lack organization.
All in all, the madCodeHook library makes a good impression and seems like a library to be used.

![Power Apps Licensing Guide [thumbnail]](/uploads/media/thumbnail-280x222-power-apps-licensing-guide.webp)
![How to Build Enterprise Software Systems [thumbnail]](/uploads/media/thumbnail-280x222-how-to-build-enterprise-software-systems.webp)
![Super Apps Review [thumbnail]](/uploads/media/thumbnail-280x222-introducing-Super-App-a-Better-Approach-to-All-in-One-Experience.webp)
![ServiceNow and Third-Party Integrations [thumbnail]](/uploads/media/thumbnail-280x222-how-to-integrate-service-now-and-third-party-systems.webp)
![Cloud Native vs. Cloud Agnostic [thumbnail]](/uploads/media/thumbnail-280x222-cloud-agnostic-vs-cloud-native-architecture-which-approach-to-choose.webp)
![DevOps Adoption Challenges [thumbnail]](/uploads/media/thumbnail-280x222-7-devops-challenges-for-efficient-adoption.webp)
![White-label Mobile Banking App [Thumbnail]](/uploads/media/thumbnail-280x222-white-label-mobile-banking-application.webp)

![Mortgages Module Flexcube [Thumbnail]](/uploads/media/thumbnail-280x222-Secrets-of-setting-up-a-mortgage-module-in-Oracle-FlexCube.webp)
![Challenges in Fine-Tuning Computer Vision Models [thumbnail]](/uploads/media/thumbnail-280x222-7-common-pitfalls-of-fine-tuning-computer-vision-models.jpg)