Building a Security Stack: AWS Security Hub, Microsoft Sentinel, or On-Premises Solutions
AWS Security Hub: Benefits and Use Cases
AWS Security Hub is a cloud security posture management (CSPM) solution, which aggregates security configurations across the monitored cloud infrastructure, alerts about misconfigurations, and provides recommendations for remediation. With a helicopter view of the infrastructure, aggregated security findings, and automatic compliance checks, companies can enforce better security practices to avoid non-compliance, data breaches, or other security events.
AWS Security Hub is not a standalone Security Information and Event Management (SIEM) solution, however. By default, it only ingests AWS-related security findings but does not directly ingest higher volume event logs, for example, from AWS CloudTrail. Likewise, AWS Security Hub does not collect security data from on-premises or other non-AWS workloads (e.g., from Azure or Google Cloud Platform).
If you want to establish better infrastructure visibility and cyber protection, you will have to integrate AWS Security Hub with other security tools such as SIEM solutions (e.g., Splunk, QRadar, ELK stack), threat detection tools, malware or fraud analytics, digital forensic solutions, etc.
Learn more about architecting and configuring AWS Security Hub.
AWS Security Hub Use Cases
The main appeal of AWS Security Hub is its wide range of integrations, which allow you to consolidate log data from the entire AWS ecosystem and external SIEM/SOAR tools in the Security Hub. Thanks to real-time data aggregation and convenient reporting dashboards, AWS Security Hub saves SOC teams hours on environment investigation and analysis. You can receive aggregated findings across AWS accounts and regions. Then auto-implement unified security rules.
Main use cases:
- Security scans across the AWS environment with status reports and remediation recommendations.
- Security monitoring against various threats: malware, DDoS attacks, and other attack vectors.
- Compliance checks against AWS cloud configuration best practices, as well as several industry directives, including Internet Security Center (CIS) and Payment Card Industry Data Security Standard (PCI DSS).
- Security analysis, based on statistical methods and correlation rules, to obtain comprehensive findings.
Integrated with other AWS and third-party tools
AWS Security Hub has native integrations with dozens of AWS services and partner products, meaning you can extend monitoring and automatic checks to multiple assets within the AWS infrastructure. Moreover, companies can implement more advanced AWS Security Hub use cases by creating integrations with third-party cybersecurity solutions.
- Aggregated user event behavioral analytics (UEBA) pertaining to different infrastructure components.
- Automatic alerting about vulnerabilities and ticket routing to the people responsible for remediation (requires integrations with incident management and SIEM tools).
- Correlate AWS Security Hub findings with each other and other log sources to establish a consolidated view and create custom alerts for curious correlations.
- Automate container vulnerability scanning within your continuous integration and continuous delivery (CI/CD) pipeline to receive alerts in your AWS Security Hub account.
Microsoft Sentinel: Benefits and Use Cases
Microsoft Sentinel is a cloud-native, converged SIEM & SOAR solution, which can be deployed across multiple cloud providers and on-premises estate. By using best-in-class artificial intelligence and machine learning algorithms, Microsoft Sentinel provides real-time threat intelligence, automated incident response, and centralized security visibility.
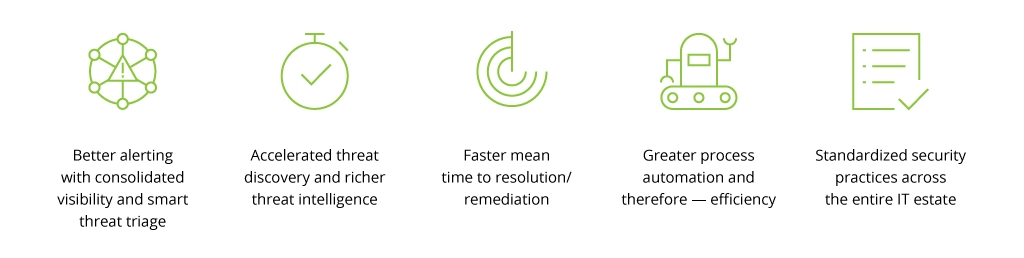
A converged cloud SIEM & SOAR setup means that there is a continuity between threat monitoring and detection on the SIEM side and incident response on the SOAR side. SOC teams that use converged SIEM/SOAR solutions benefit from:
While AWS Security Hub only protects AWS assets, Microsoft Sentinel can deliver comprehensive security analytics and threat intelligence across multi-cloud or hybrid environments.
Why Choose Microsoft Sentinel:
- Convenient integration. Microsoft Sentinel has an effortlessly simple configuration process. There is a one-click integration with all cloud components and two/three-click integration with on-premises Microsoft and Linux components. Moreover, Microsoft provides a host of bidirectional integrations with other security products for identity management, network monitoring, endpoint protection, and cloud access security brokers among others.
- Multi-cloud capabilities. Organizations can easily scale Microsoft Sentinel deployment across other popular cloud service providers (e.g., AWS, Google Cloud Platform), using native connectors and extensive documentation. In other words: You can establish a cloud-agnostic strategy without worrying about extra risk exposure.
- Built-in controllers for Microsoft and Azure environments. Sentinel automatically establishes recommended security configurations and policies, based on the company’s best practices for different types of assets and environments. This means less manual work for your SOC team and faster time-to-value.
- Substantial knowledge base. Even if you opt to integrate third-party security or non-security tools, Microsoft still comes through with an all-around knowledge base. There are plenty of playbooks and runbooks available for different integration and deployment scenarios, meaning your teams always have the necessary security context for doing their job.
- Cost-effective, especially if you are already in the Azure cloud. A certain percentage of free traffic monitoring via Microsoft Sentinel is already included with each Azure license. Moreover, users report that Microsoft Sentinel tends to be 48% more cost-effective than their legacy SIEM on average.
Learn more about Microsoft Sentinel adoption scenarios.
Microsoft Sentinel Use Cases
Microsoft Sentinel offers a unified solution for security monitoring, threat detection, proactive threat hunting, and rapid threat response. Moreover, Sentinel's capabilities can be further extended to facilitate vulnerability management (by ingesting data from a Threat & Vulnerability Management platform) or risk management (e.g., by ingesting logs from Microsoft 365 and Microsoft Graph) or pursue a number of other use cases.
A case in point: a Swiss manufacturing company already relied heavily on the Microsoft ecosystem, therefore Infopulse advised SOC implementation using Microsoft Sentinel capabilities. With a new system in place, the company detects and resolves over 500 security incidents per month, thanks to a 24/7 monitoring and vulnerability scanning process, implemented across its branches in Central Europe, Asia, and North and South America.
Key use cases:
- All-embracing security data collection. Source, filter, transform, and enrich security data from every asset in your IT estate. Track events via convenient visual dashboards and segmentable analytics reports. With over 200+ native and partner connectors, you can source any type of data with Sentinel.
- Rapidly identifying the source and scope of the incident. Thanks to smart alert triage, your SOC staff gets instantly notified about system anomalies and potential incident types. Advanced threat intelligence algorithms also help them establish the attack tactics, techniques, and procedures (TTPs), plus assess (and limit) the impact of the incident on your organization.
- Streamlined response to security incidents. With Microsoft Sentinel Notebooks and Playbooks templates, security teams can automate repetitive tasks, perform advanced analysis, and create custom detections and remediation workflows in less time.
- Proactive threat hunting. Identifying threats before they occur with an in-built hunting search and query tools, which can access all connected data sources. A convenient hunting dashboard enables your teams to run investigations in minutes and receive aggregated insights in one place.
Read more about sample Microsoft Sentinel use cases.
Use Cases of On-Premises SIEM/SOAR Solutions
Although organizations have been proactively choosing to become cloud-first, on-premises infrastructure still plays a key role in some instances. For example, regulatory requirements in your industry may mandate on-premises data storage (and prohibit or limit the usage of public cloud resources). Likewise, certain industries must maintain extra low latency for critical workloads, which is easier to enable with on-premises infrastructure. Finally, there are instances when virtualizing an asset is merely impossible (e.g., a hardware controller of a Wi-Fi network).
All of the above on-premises assets require security protection — and that is when solutions like QRadar and Splunk come in handy. Both support the following on-premises security monitoring scenarios:
- Firewall rule management
- Network traffic monitoring
- User behavior analytics
- Security data analysis
- Incident management
- Compliance reporting
The common issue of on-premises SIEM/SOAR deployments, however, is that the collected data remains isolated and — therefore requires separate analysis and attention. To consolidate monitoring across hybrid infrastructure without moving any sensitive data, you can use Azure Arc service to establish a bilateral data exchange bridge between local and cloud-based systems. In this way, you can resurface security data from on-premises systems to a cloud-based SIEM/SOAR solution and dispatch back security and governance configurations.
Final Thoughts
To establish a robust security perimeter, organizations need three components:
- Solutions for data collection on the end-systems
- Aggregators for data filtering, transformation, and enrichment for multiple systems
- Purpose-based solutions for various security use cases (e.g., threat detection, investigation, remediation, etc.).
In a nutshell, the above represents the optimal SIEM/SOAR architecture, which can include multiple auxiliary tools apart from the core solution. For example, extra local log aggregators, server‑side data processing pipelines, premium data enrichment tools, or open-source data visualization apps.
The setup will differ based on your IT infrastructure design, selected SOC use cases, and wider regulatory and compliance requirements. Based on the security assessment, a qualified security architect should propose a reference architecture for your SIEM/SOAR deployment and then facilitate the implementation of the proposed solution(s), workflows, and playbooks.
![Security Stack: use cases [main banner]](https://www.infopulse.com/uploads/media/BANNER~1.WEB)


![SOC Use Cases [thumbnail]](/uploads/media/thumbnail-280x222-soc-use-cases-definition-and-implementation-best-practices.webp)
![AWS Security Hub Integrations [thumbnail]](/uploads/media/top-security-solutions-to-integrate-with-aws-security-hub-for-soc-280x222.webp)
![SOC Adoption Scenarios [thumbnail]](/uploads/media/three-ways-to-introduce-SOC-to-your-organization-280x222.webp)
![Microsoft Sentinel Test Cases [thumbnail]](/uploads/media/5-test-use-cases-of-ms-sentinel-implementation-280x222.webp)
![Microsoft Sentinel Adoption Guide [thumbnail]](/uploads/media/azure-sentinel-how-to-ensure-seamless-integration-and-optimize-your-soc-licensing-costs-280x222.webp)
![SIEM & SOAR Tools [thumbnail]](/uploads/media/siem-and-soar-tools-a-gentle-guide-to-selecting-the-right-solution-280x222.webp)




